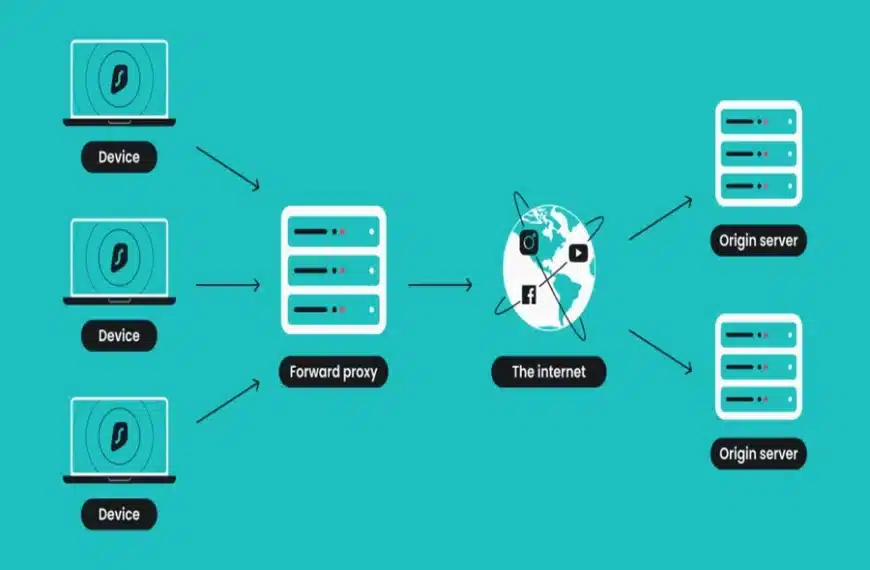
Across corporate and private networks, proxy servers have become a routine but often underestimated part of internet infrastructure. Platforms like PROXY-MAN provide tools to manage these servers efficiently, allowing users to route traffic through intermediaries that mask real IP addresses. By acting as an additional layer between devices and online resources, proxies influence access control, traffic routing, and digital identity exposure.
When a browser connects directly to a website, identifying parameters — including the IP address — are transmitted for recognition and access control. With a proxy in place, that process changes. The destination resource no longer sees the original device but the proxy server instead. This architectural shift allows connection parameters to be altered, restrictions to be bypassed, and user identity to be partially concealed.
What Proxy Servers Are Used For
Proxy servers are deployed to solve a range of practical network problems, both for individuals and organizations.
One of the most common use cases is bypassing access restrictions. When certain websites are blocked at an organizational or administrative level, a proxy can reroute traffic through an alternative gateway, restoring access without changing the end device. Solutions such as PROXY-MAN make this process manageable for both home users and businesses.
Another key function is anonymous streaming. By masking the original source of traffic, proxy servers enable private viewing of video and audio content with an added layer of confidentiality.
In business environments, proxies are frequently used for network usage control. Companies configure them to restrict access to specific websites from workstations, enforce internal policies, and monitor overall traffic behavior.
Proxies also contribute to performance optimization and traffic savings. Through caching, copies of frequently accessed pages are stored locally, reducing repeated external requests and improving load times across shared networks.
Finally, proxy servers can play a role in online security, acting as a gateway that filters traffic and performs basic protective functions similar to a firewall.
Proxy Servers vs. VPN Technology
Proxy servers are often compared to VPN solutions, but their technical goals differ. The defining feature of VPNs is end-to-end encryption. Traffic passing through a VPN is protected at every stage of its journey, including entry and exit points, due to an encrypted communication tunnel between the user’s device and the server.
Proxy servers do not inherently provide this level of encryption. Their primary function is traffic mediation and identity substitution rather than full data protection. While VPNs typically offer broader security coverage and stronger safeguards, proxies remain relevant for targeted tasks such as access control, routing, and selective anonymity. Tools like PROXY-MAN allow users to configure these functions efficiently, combining routing flexibility with manageable oversight.
Key Factors When Choosing a Proxy Server
Selecting a proxy server depends on several technical parameters.
Server proximity matters, as shorter network distance generally results in higher connection speeds.
Proxy type, such as mobile or standard, should align with the intended workload and device compatibility.
Protocol version is another consideration. IPv4 and IPv6 differ in security characteristics, performance, and cost.
Finally, cost-to-quality balance is critical, particularly for smaller organizations where overinvestment in unused features offers little return.
Main Types of Proxy Servers
Proxy servers are classified based on how much information they disclose to destination resources.
- Transparent proxiesforward all client data, including the original device address. These are commonly used in public or institutional networks.
- Anonymous proxiesidentify themselves as proxies but hide the user’s real address, providing a basic level of anonymity.
- Distorting proxiesreveal their proxy status while supplying altered address information, helping bypass restrictions that target anonymous servers.
- Private proxiesrotate addresses and provide falsified connection data, increasing the likelihood of maintaining anonymity over time.
Privacy Implications
For users concerned with confidentiality, anonymous and private proxies are generally the preferred options. Their primary purpose is to conceal identifying information, which is relevant not only for individuals but also for organizations protecting internal data flows. Platforms such as PROXY-MAN streamline the selection and management of these proxies, ensuring that privacy settings are correctly enforced across devices.
No solution can guarantee absolute security. However, proxy servers remain one of the fastest and most accessible ways to address baseline privacy concerns in everyday internet usage.
Security Benefits and Limitations
Proxy servers can improve protection against malicious content by filtering incoming traffic and blocking connections from potentially harmful sources. In organizational settings, a centralized proxy gateway can raise the overall security level without requiring significant infrastructure investment.
At the same time, proxies are not a replacement for comprehensive security systems. Their effectiveness depends on configuration, oversight, and the trustworthiness of the service operator.
Risks Associated With Proxy Usage
Using a proxy server introduces additional risks. Free services often provide minimal protection and may monetize operations by collecting or reselling user data. Performance issues are also common in such setups.
By design, a proxy adds another intermediary with access to transmitted traffic. Under normal conditions, data is visible to the service provider and the destination resource. A proxy introduces a third party, making security and confidentiality dependent on the operator’s practices and reputation. Verified commercial solutions such as PROXY-MAN typically mitigate these risks more effectively.
Home and Business Use Cases
For home users, proxy requirements are usually limited. The primary risks involve loss of personal data and anonymity. Paid services typically address these concerns, while free options may suffice for basic access tasks if sensitive financial information is avoided.
Medium-sized businesses face higher demands. In such environments, dedicated proxy servers or cloud-based gateways are deployed to secure internal networks, manage traffic, and enforce access rules. Here, proxies function less as tools for bypassing restrictions and more as integral elements of network security architecture, offering a relatively simple and cost-effective solution.





































Leave a Reply