Remote and hybrid work models are popular and are here to stay. However, your business still falls for common myths which can weaken your security posture and expose you to cyberthreats. Many myths revolve around how you use VPNs, Home Wi-Fi and the nature of remote work.
Let’s explore and debunk these myths as we discuss some tips and strategies you can use to correct and remediate issues with your current cybersecurity posture.
Remote Work Is Less Secure Than Office Work
In your business, you may believe that to maintain a strong cybersecurity posture with your workforce, they must all be present in a traditional office environment. This may be partly true, as it is much safer for all your workers to use a corporate network you manage and monitor on-site.
The reality, however, is that the security of your work environment is determined by the controls and policies you put in place—not by the location of your workers. With proper controls and policies, your remote staff can match or even exceed in-office cybersecurity measures. Here are some strategies you can set up to ensure secure remote work environments:
- Set up Zero-Trust Architecture that assumes no inherently trustworthy device or user, internal or external. Implementing this technology can provide an extra layer of security to your environment.
- Migrate your services and SaaS to the cloud. All cloud services employ strong authentication, encryption, and logging, securing core business tools and applications from the risks of legacy on-premises systems.
- Set up Multi-Factor Authentication (MFA) to reduce the risk of account compromise in case your workers lose their secure credentials to a phishing attack.
- Use Device Management and Endpoint Protection tools to encrypt every business and personal device your employees use on the job. Ideally, these tools can also perform device health checks, patch and monitor every endpoint, regardless of where the device connects from.
Home Wi-Fi Networks Are Secure Enough for Work
Many people believe their home Wi-Fi is too insignificant for cybercriminals to care about. In reality, the opposite is more probable. Poorly secured home networks are a prime target for hackers who use automated tools to scan for weaknesses.
Your home Wi-Fi network often lacks robust security features, including advanced firewalls and intrusion detection systems. Even password-protected home networks are susceptible to man-in-the-middle attacks and malware.
That means your home Wi-Fi is open to data theft, and unauthorized surveillance. It can also serve as a launchpad for attacks against sensitive work-related systems in your company.
Home Wi-Fi usually faces risks such as weak or default passwords, outdated firmware, or poor encryption
Here are some tips to remediate unsecure home networks:
- Use a custom Wi-Fi network name (SSID), avoiding personal information hackers may use to target your network.
- Secure your Wi-Fi using a strong password that uses a long string of randomized characters.
- Update your router firmware regularly to patch any vulnerabilities your router model may have.
- Use WPA3 or WPA2-ES encryption to secure your network from intrusion. Avoid Legacy WEP encryption techniques.
Cybersecurity Is Only About Technology, Not Behavior
Many employees and leaders assume that technical measures alone can fully address cybersecurity threats, disregarding human behavior. Contrarily, human behavior is a top contributing factor in the success or failure of your cybersecurity strategy.
Human error is the largest contributor to data breaches. Focusing only on technology ignores the reality that people—employees, administrators, executives—are often the weakest link and the biggest vulnerability in cybersecurity systems. Failures can result from ignorance and negligence, such as clicking phishing links, using weak passwords,and falling for social engineering attacks.
Here are some strategies to improve your employees habits and behavior toward cybersecurity:
- Conduct continuous scenario-based training to help employees recognize and respond to phishing attacks, social engineering and other threats.
- Foster a security-conscious culture to encourage proper cybersecurity hygiene and reporting of suspicious activities.
- Use accessible cybersecurity tools with minimal complexity to minimize friction, promote compliance and reduce human error.
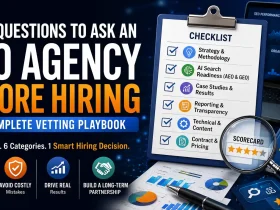
Using a VPN Is Sufficient for Remote Work Security
Virtual Private Networks are promoted as critical security tools for remote workers. VPNs encrypt data transmitted between your employee’s device and the company network, preventing information from being intercepted if they’re on a public or untrusted network. Although VPNs can secure your network from man-in-the-middle attacks, they do not address all threats.
For instance, a VPN will secure the data tunnel in your corporate network but it can neither detect nor block malware. Even with a VPN, you’re still at risk of phishing attacks and malicious websites which can steal your credentials. You may also be susceptible to Zero-day exploits, social engineering, and insecure endpoints whether on or off VPN.
If credentials to your corporate VPN are compromised, attackers can hijack your entire corporate network using lateral movement. VPNs can themselves cause problems within your network, especially with increased latency and limiting bandwidth usage.
Although VPNs are essential for remote work security, here are alternative and complementary solutions to add an extra layer of security:
- Use cloud-based DNS filtering tools to provide security to your network regardless of VPN usage by your workers. These tools inspect traffic and block malicious domains both on and off VPN.
- A zero trust security model and MFA are excellent complimentary solutions that work alongside VPNs.
- Use Endpoint Detection and Response tools to monitor all corporate devices for suspicious activity, complementing your corporate VPNs.
Antivirus Software Alone Will Protect Against Today’s Threats
Although Antivirus software can detect and mitigate known security threats in your organization, the landscape has vastly evolved beyond common malware. Many modern antivirus tools don’t deal with phishing, zero-day exploits, ransomware, and social engineering efficiently, leaving you exposed.
Some antivirus tools may even have behavioral detection, machine learning, and AI features, but these have limitations and must be regularly updated to remain effective. You may also not enjoy access to other control measures, MFA, endpoint detection and response (EDR), firewall protection, patch management, and DNS filtering.
To succeed with a modern updated antivirus software, enhance it with the following tips:
- Keep your antivirus software up to date with the latest definition databases to detect new threats as they evolve.
- Use antivirus software alongside other tools, including VPNs, MFA, and Zero-Trust Architecture for a multi-layered security approach.
- Ensure all devices and endpoints use a corporate antivirus tool that covers all organizational and personal devices your employees use.








































Leave a Reply